How does R2-D2 know who obi-Wan Kenobi is?
How does he decide to play the recording of Princess Leia for obi-Wan, but not Luke?
Threats: What Every Engineer Should Learn From Star Wars provides a fun and jargon-free introduction to crucial cybersecurity knowledge for everyone involved in the development of software and systems. The Star Wars franchise offers an accessible set of examples of real world cyber threats.
Hover or
Tap / Hold
to reveal
the cover
For over a decade, Adam Shostack, author of the highly regarded and successful Threat Modeling: Designing for Security, has been using lessons from Star Wars to teach about security. Threats serves everyone involved in building complex technology, even if it’s not their most desperate hour.
The book, which releases February, 2023 is about what every engineer needs to know (like it says on the cover). Security has become a fundamental requirement for new systems, but that doesn't mean it's easy to grapple with. This book is engineered to provide readers with a broad set of fundamental knowledge in a fun and engaging way.
Security matters in 2023, and it's often confusing and overwhelming. Many people start teaching from threats like SQL injection or cross site scripting, or showing you assembly code. In contrast, Threats starts with the question: How does R2-D2 decide to show the hologram to Ben Kenobi but not Luke Skywalker? The answer is authentication, which is how we address the threat of spoofing. You'll learn how computers authenticate people, and how people authenticate computers, and the specific threats to each. By starting with the broad ideas, the book teaches a framework that will serve engineers through their career.
These threats apply to all technological systems, and center on the computerized ones — the hardware and software. Civil engineers, mechanical engineers and others may yearn for the more elegant systems from a less computerized time, but even their systems are increasingly computerized and connected.
Timeless Threats
The brain is an amazing machine for analogizing, which is why fictional examples help us learn complex or abstract concepts. Just like there are timeless tropes in fiction, there are broad, timeless sets of threats.
Using examples from both Star Wars and real life, Adam teaches readers how to find security problems as they build systems. Readers will learn to organize vast amounts of security information into smaller, more manageable pieces.
What You Will Learn
- Which timeless threats keep raising their ugly heads
- The concrete details and true stories of where those threats have emerged (struck? manifested?)
- A framework for organizing the complex, sprawling world of security threats
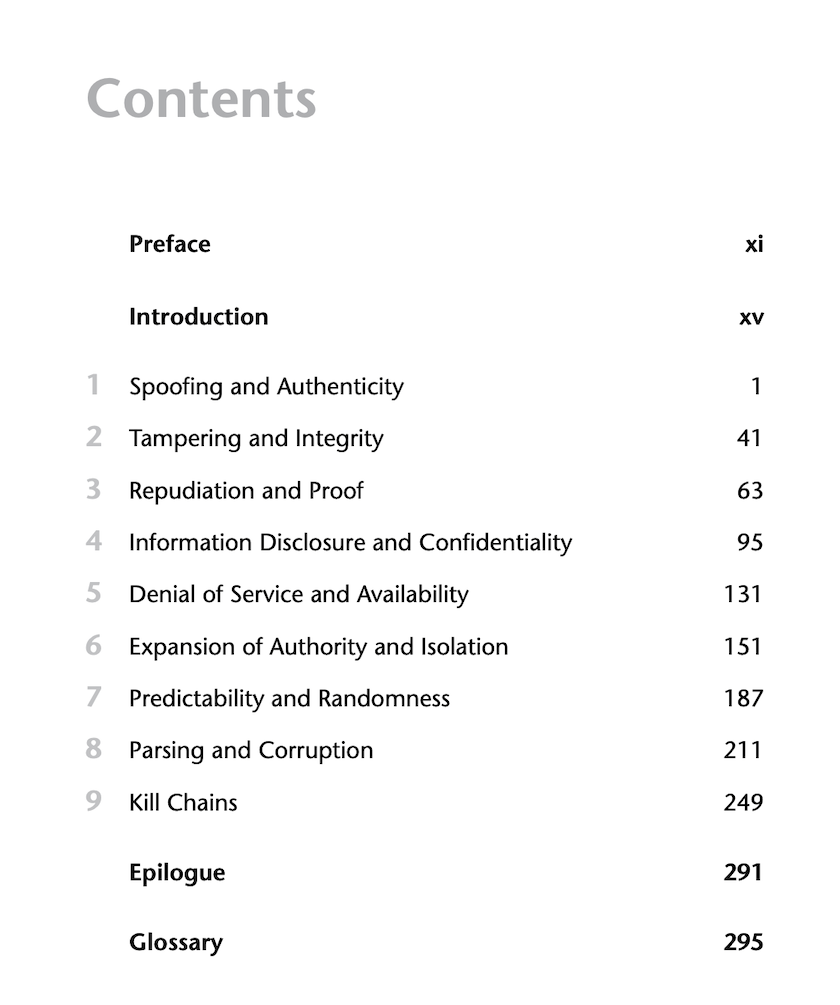
Each chapter is devoted to a threat. And like the Force, each threat has a light side and a dark side. For example, the book opens with Spoofing and Authenticity. But unlike the Force, we don't hope for balance. We hope to understand the threat, because that's the best way to anticipate and address the threat, and bring peace to the galaxy. (Or so we hope.) You can read a sample chapter here.
How to get the book
- You can buy paper copies on Amazon or wherever fine books are sold.
- Amazon also has a Kindle version, Kobo has an epub.
- An audio book is available from Audiobooks.com.
- An Italian edition is available from Apogeo
You can also sign up for updates. You can sign up for just announcements or to hear about other educational content from Adam including courses.
Subscribe for Updates
Complete the form below to get Adam’s latest updates about his book, blogs, and new training opportunities.